TL;DR Opendkim. Hats off the to folk who do marvelous packing 99.99999% percent of the time.
But sometimes they just get it wrong or at least all documentation regarding the package, does not match up with the behavior the packager intended.
That said, hopefully i will help solve some of these issues here.
I assume you have postfix already working and you are just looking to add dkim support.
Install opendkim
apt-get install opendkim opendkim-toolsConfigure systemd service file
cat > /lib/systemd/system/opendkim.service <<EOT
[Unit]
Description=OpenDKIM DomainKeys Identified Mail (DKIM) Milter
Documentation=man:opendkim(8) man:opendkim.conf(5) man:opendkim-genkey(8) man:opendkim-genzone(8) man:opendkim-testadsp(8) man:opendkim-testkey http://www.opendkim.org/docs.html
After=network.target nss-lookup.target
[Service]
EnvironmentFile=/etc/default/opendkim
Type=forking
PIDFile=/var/run/opendkim/opendkim.pid
User=opendkim
ExecStart=/usr/sbin/opendkim -P /var/run/opendkim/opendkim.pid -p $SOCKET
Restart=on-failure
ExecReload=/bin/kill -USR1 $MAINPID
[Install]
WantedBy=multi-user.target
EOTThe specific changes here are lines #9 EnvironmentFile #13 -p $SOCKET
Defaults File
cat > /etc/default/opendkim <<EOT
SOCKET="inet:12301@localhost"
EOTOpendkim Config file
cat > /etc/opendkim <<EOT
Mode sv
Syslog yes
SyslogSuccess yes
LogWhy yes
#Socket inet:12301@localhost
Umask 002
SendReports yes
SoftwareHeader yes
Canonicalization relaxed/relaxed
Selector default
MinimumKeyBits 1024
KeyTable refile:/etc/dkimkeys/KeyTable
SigningTable refile:/etc/dkimkeys/SigningTable
ExternalIgnoreList refile:/etc/dkimkeys/TrustedHosts
OversignHeaders From
TrustAnchorFile /usr/share/dns/root.key
EOTSpecific changes here are lines #7 hashed out socket file, it simply does not work.
The only way to get opendkim to honour this setting is passing it to the command line #13 of the service file.
Modify /etc/postfix/main.cf and add/edit the following lines
smtpd_milters = inet:localhost:12301
non_smtpd_milters = inet:localhost:12301Create referenced folders for your open dkim keys
mkdir -vp /etc/dkimkeys/keysTrustedHosts
cat > /etc/dkimkeys/TrustHosts <<EOT
127.0.0.1
::1
localhost
example.com
*.exmaple.com
EOTSingingTable
cat > /etc/dkimkeys/SigningTable <<EOT
*@exmaple.com default._domainkey.example.com
EOTKeyTable
cat> /etc/dkimkeys/KeyTable <<EOT
default._domainkey.example.com example.com:default:/etc/dkimkeys/keys/default.private
EOTCreate private/public key for signing
cd /etc/dkimkeys/keys
opendkim-genkey -s default
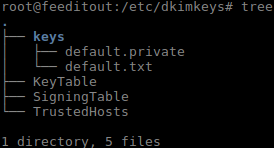
Your directory should now look like this
Tell systemd to reload the the daemon files and restart
systemctl daemon-reload
systemctl restart opendkim
systemctl restart postfixDNS
Now go modify your DNS, adding a TXT record ‘default._domainkey’.
Copy and paste everything between the parenthesis. ( everything here ) into the value field of the TXT record
cat keys/default.txt
default._dkim IN TXT ( "v=DKIM1; k=rsa; "
"p=MIGfMA0GCSqGSIGNA....BIG LONG DIRTY HASH ....ciaxOhS24T4MFwIDAQAB" ) ; ----- DKIM key default for com
Enjoy
Other resources
https://www.google.com/search?q=opendkim+setup
